“Chabada” is here to safeguard your smartphone from malicious Android apps
Uncategorized
 With growth in upcoming apps, there comes a very obvious possibility of getting your phone infected with faux apps. Currently the trend of Smart phones has settled in highly. These smart phones possess either Android OS, Blackberry OS, iOS, Symbian, etc… These operating systems are offering a wide range of mobile applications which can be easily downloaded and viewed in a couple of minutes. Currently there are numerous portals that assist the users in downloading the apps. But it is very essential for the users to check the point of downloading. There are various vendors who even provide malicious apps for the smart phones. But the question here comes is How to identify the malicious app and safeguard the device? Thus new software named “Chabada” has been developed which helps the user in identifying the wicked Android app for smartphones.
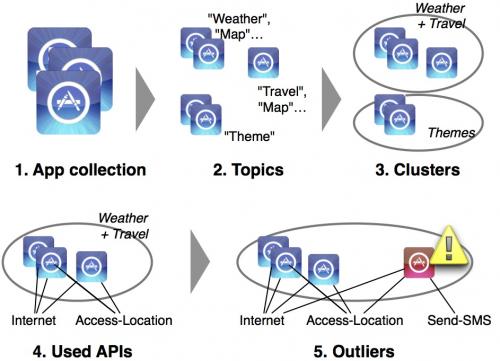
Chabada identifies the source of wrong apps and gives a detailed description to the user about it. It analyses the app in great detail and then come up with its conclusion. Chabada reads every app that is available in the app store. The software identifies every language. It identifies apps with titles like music, travel, food, shopping, etc. Chabada forms clusters of the apps matching to such headers. Then it studies every cluster individually. The app that it finds to be suspecting is notified to the user.
Chabada has been developed by Andreas Zeller who teaches software engineering at the Saarland University located in Germany. He said that, “Apps whose functionality is described in the app store should behave accordingly. If that is not the case, they are suspect.” The research team of Andreas had applied Chabada on the Google Play Store. It analyzed 22521 apps from it. Chabada uses Cluster analysis in this process. The app is found to be faux if it sends out secret text messages. Zeller explained this point by giving an example of travel apps. He said that “Like travel apps normally access the current location and a server to load a map. So a travel app secretly sending text messages is suspicious.”
The software Chabada is getting developed to a further level. The research team of Andreas is making it capable enough of preventing the malicious apps from even entering the Apps stores. Zeller quoted, “In the long run, ‘Chabada’ might operate in the form of a gatekeeper, making certain that malicious apps can never build it into an app store.”
The common man is unaware of the spy apps that are lying in the apps store. Hence, they get downloaded unknowingly and can lead to further problems for the user. Chabada detects spy apps even without having any information about them. The apps that are questioning lie as outliers outside the clusters. Chabada will indeed gain a first mover advantage in this segment. Zeller has been invited by great software giants for applying Chabada for their apps. Google will be utilizing Chabada for identifying any malwares in its Google Play Store.
Image credit: http://phys.org
With growth in upcoming apps, there comes a very obvious possibility of getting your phone infected with faux apps. Currently the trend of Smart phones has settled in highly. These smart phones possess either Android OS, Blackberry OS, iOS, Symbian, etc… These operating systems are offering a wide range of mobile applications which can be easily downloaded and viewed in a couple of minutes. Currently there are numerous portals that assist the users in downloading the apps. But it is very essential for the users to check the point of downloading. There are various vendors who even provide malicious apps for the smart phones. But the question here comes is How to identify the malicious app and safeguard the device? Thus new software named “Chabada” has been developed which helps the user in identifying the wicked Android app for smartphones.
Chabada identifies the source of wrong apps and gives a detailed description to the user about it. It analyses the app in great detail and then come up with its conclusion. Chabada reads every app that is available in the app store. The software identifies every language. It identifies apps with titles like music, travel, food, shopping, etc. Chabada forms clusters of the apps matching to such headers. Then it studies every cluster individually. The app that it finds to be suspecting is notified to the user.
Chabada has been developed by Andreas Zeller who teaches software engineering at the Saarland University located in Germany. He said that, “Apps whose functionality is described in the app store should behave accordingly. If that is not the case, they are suspect.” The research team of Andreas had applied Chabada on the Google Play Store. It analyzed 22521 apps from it. Chabada uses Cluster analysis in this process. The app is found to be faux if it sends out secret text messages. Zeller explained this point by giving an example of travel apps. He said that “Like travel apps normally access the current location and a server to load a map. So a travel app secretly sending text messages is suspicious.”
The software Chabada is getting developed to a further level. The research team of Andreas is making it capable enough of preventing the malicious apps from even entering the Apps stores. Zeller quoted, “In the long run, ‘Chabada’ might operate in the form of a gatekeeper, making certain that malicious apps can never build it into an app store.”
The common man is unaware of the spy apps that are lying in the apps store. Hence, they get downloaded unknowingly and can lead to further problems for the user. Chabada detects spy apps even without having any information about them. The apps that are questioning lie as outliers outside the clusters. Chabada will indeed gain a first mover advantage in this segment. Zeller has been invited by great software giants for applying Chabada for their apps. Google will be utilizing Chabada for identifying any malwares in its Google Play Store.
Image credit: http://phys.org Frequently Asked Questions?

01
Tech Gadgets
Apple Pencil Pro: A Game-Changer for Artists, Designers & Note-Takers
May 8, 2024

01
AR and VR
Snap Engages Users with New AR & ML Toolkit
May 7, 2024

01
Tech Gadgets
Power Down to Power Up: How a Digital Detox Benefits You and the Planet
May 6, 2024

01
Mobile Technology
iPhone Repair Just Got Easier: No More Disabling Find My Before Service
May 4, 2024
SUSBSCRIBE TO OUR NEWSLETTER
Join our subscribers list to get the latest news and special offers.
Apple Pencil Pro: A Game-Changer for Artists, Designers & Note-Takers
Snap Engages Users with New AR & ML Toolkit
Power Down to Power Up: How a Digital Detox Benefits You and the Planet
Gatherings Just Got Easier: WhatsApp Communities Now Have Built-In Event Planning