No Indicator Lights Anymore for Mac Camera Recording
Uncategorized
 As with just about all the rest of the modern hardware piece, the webcams present in computers, which the researchers took a close look at, especially those 2008-vintage Mac Books, iMac G5, Mac Book Pros, and Intel iMacs are those smart devices having integrated processors and software of their own. The webcams consists of three integral components: an USB interface chip having both 8051-compatible microcontroller and an integrated Intel and little RAM as well as some amount of EEPROM memory and image sensor.
One line which connects the USB chip to imaging sensor input is called standby. As the interface chip holds the line high, the sensor transits into standby mode and quits the data production. When the interface chip holds it low, the sensor moves out of standby mode and initiates the data production. Even the LED’s negative side is wired with the same line. In regards with this, image chip is off thereby turning off the LED. When the line is held high and the image chip is on thereby turning on the LED when the line is held low.
In this principle, the process is said to act like a hardware interlock. The LED is neatly hardwired, with its state directly reflecting if the imaging chip is in the standby mode or not. But, the entire system is manipulated by a software layer unfortunately. When webcam is loaded from the driver, the host of the PC uploads a little program to an USB controller. This has no permanent personal firmware storage; therefore, it has to be uploaded on every camera. This little program in the turn configures the image chip. The imaging chip falls short of a lot many configurable properties, but it needs to keep an account of whether it pays any standby input attention.
Apple’s personal drivers form a configuration wherein the standby mode earns much importance. Apart from this, rest of the configurations is possible. These configurations could be like the one wherein the chip is less attentive towards standby completely and always produces the image data. Bearing this knowledge in mind, the researchers had written a fresh piece of software for the webcam upload. This software piece was pretty similar to that of software in normal webcam. Yet, there were two variations: primarily, the imaging sensor ignores the standby input and secondly, ensures that the standby line would always be held high for the LED prevention from illuminating. The outcome is a webcam built with hardwired LED indicator that nevertheless allowed capturing of an image without any LED indicator blinking.
Regardless of this design being sensible for several users, provided the apparent surreptitious abundance of webcam, its capability of spying is not that vivid as per the researchers’ testing of modern Apple computers or those from other brands termed as non-Apple webcams. Protective designs for the LED indicator are possible, and various other USB controller pairings or imaging sensors might prove to be additionally robust.
As with just about all the rest of the modern hardware piece, the webcams present in computers, which the researchers took a close look at, especially those 2008-vintage Mac Books, iMac G5, Mac Book Pros, and Intel iMacs are those smart devices having integrated processors and software of their own. The webcams consists of three integral components: an USB interface chip having both 8051-compatible microcontroller and an integrated Intel and little RAM as well as some amount of EEPROM memory and image sensor.
One line which connects the USB chip to imaging sensor input is called standby. As the interface chip holds the line high, the sensor transits into standby mode and quits the data production. When the interface chip holds it low, the sensor moves out of standby mode and initiates the data production. Even the LED’s negative side is wired with the same line. In regards with this, image chip is off thereby turning off the LED. When the line is held high and the image chip is on thereby turning on the LED when the line is held low.
In this principle, the process is said to act like a hardware interlock. The LED is neatly hardwired, with its state directly reflecting if the imaging chip is in the standby mode or not. But, the entire system is manipulated by a software layer unfortunately. When webcam is loaded from the driver, the host of the PC uploads a little program to an USB controller. This has no permanent personal firmware storage; therefore, it has to be uploaded on every camera. This little program in the turn configures the image chip. The imaging chip falls short of a lot many configurable properties, but it needs to keep an account of whether it pays any standby input attention.
Apple’s personal drivers form a configuration wherein the standby mode earns much importance. Apart from this, rest of the configurations is possible. These configurations could be like the one wherein the chip is less attentive towards standby completely and always produces the image data. Bearing this knowledge in mind, the researchers had written a fresh piece of software for the webcam upload. This software piece was pretty similar to that of software in normal webcam. Yet, there were two variations: primarily, the imaging sensor ignores the standby input and secondly, ensures that the standby line would always be held high for the LED prevention from illuminating. The outcome is a webcam built with hardwired LED indicator that nevertheless allowed capturing of an image without any LED indicator blinking.
Regardless of this design being sensible for several users, provided the apparent surreptitious abundance of webcam, its capability of spying is not that vivid as per the researchers’ testing of modern Apple computers or those from other brands termed as non-Apple webcams. Protective designs for the LED indicator are possible, and various other USB controller pairings or imaging sensors might prove to be additionally robust.
Frequently Asked Questions?
01
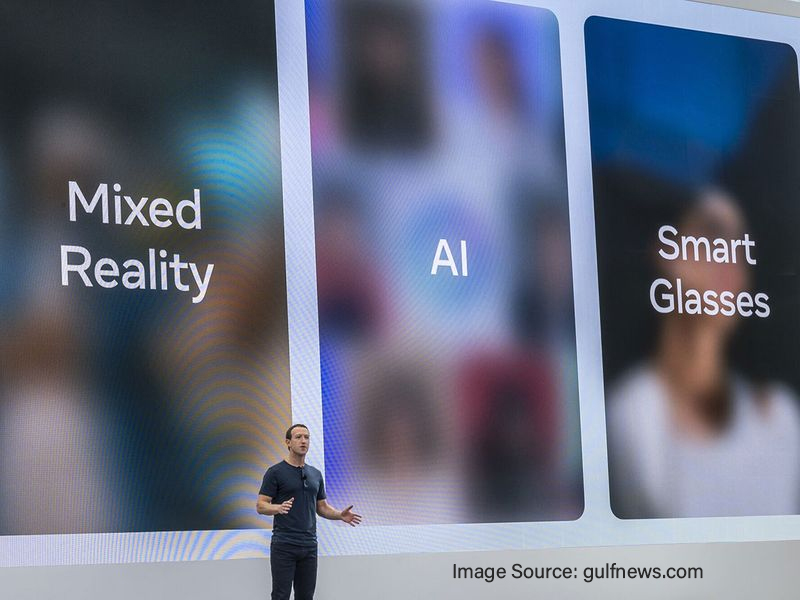
AR and VR
The Quest 3 Gets Personal: Unveiling Meta AI’s Assistant for VR
Jul 26, 2024

01
Tech news
Third-Party Cookie Crumble? Google Reverses Course, Keeping Cookies in Chrome
Jul 25, 2024

01
AI & ML
The Power of Creation, the Price of Privacy: Top Risks of Generative AI
Jul 24, 2024

01
Cybersecurity
Decoding the Disruption: Recent Microsoft Outage and Its Global Impact
Jul 22, 2024
The Quest 3 Gets Personal: Unveiling Meta AI’s Assistant for VR
Third-Party Cookie Crumble? Google Reverses Course, Keeping Cookies in Chrome
The Power of Creation, the Price of Privacy: Top Risks of Generative AI
GPT-4o Mini: Unveiling OpenAI’s Accessible AI Powerhouse